 |
Interesting Articles about Popular Topics |
|
|
Dave Carlson - July 31, 2006 Computer forensics is an emerging industry, fueled by rising computer crime and a litigious society. The primary tenant of the industry is to discover and preserve data stored on electronic devices so it can be used as evidence in a court of law. This paper explores organization management, industry challenges, and business opportunities in a new and rapidly developing industry. It concludes with thoughts about future business possibilities and anticipated management trends of the industry. Evolution of computer forensics industry management practices will parallel main-stream business enterprises to meet future challenges. Companies which offer computer forensic investigation services will succeed if they follow best practice management techniques for a company of their size and location. Computers, electronic storage, and communication devices abound in our society. With advancements in technology come societal parasites who use technology to conduct criminal activities. Criminals use technology to hide incriminating evidence or contraband materials (Secret Service, 2006, ¶ 3). The industry emerging to meet new technology crime challenges facing todays law enforcement agencies is computer forensics. The first recorded use of the term computer forensics was in 1991 during a training session sponsored by the International Association of Computer Specialists (IACIS) in Portland, Oregon (Armor Forensics, 2005, ¶ 1). A widely-accepted definition of computer forensics is the scientific examination and analysis of data held on, or retrieved from, computer storage media in such a way that the information can be used as evidence in a court of law (DIBS, 2006, ¶ 4). Its purpose is to determine if there is potential evidence stored in a computer or other electronic device that can be used in court following accepted rules of evidence (Robbins, n.d., ¶ 1). Hall (2006) identifies computer forensics companies as the private investigators of cyberspace (¶ 4). (See Figure 1) 
Figure 1. Computer forensics. (Michailov, 2006) This article will explore computer forensics industry management along with current challenges and opportunities. It will conclude with a speculative discussion of evolutionary paths the industrys business management may follow in the future. The computer forensics industry is comprised primarily of three types of business entities: sole practitioner, specialized company, and related company. These three entities share management traits, but each has its own unique characteristics and challenges. All are concerned about managing customer expectations, specialized training, marketing requirements, and a myriad of other management tasks. Sole PractitionerA sole practitioner is a single individual, frequently organized as a proprietorship or Limited Liability Company. An example of a successful sole practitioner is Jon Berryhill. Jon and his wife Kate operate Berryhill Computer Forensics, LLC in Benicia, California. Founded in 1997, the company provides computer forensics services to attorneys, private investigators, litigation support firms, law enforcement/government agencies, corporations and small businesses (Berryhill, 2005, ¶ 1). As with any one-man show, Berryhill Computer Forensics faces a finite growth potentialJon can be in only one place at a time. Specialized CompanyA specialized company can be any size, but almost exclusively does business in the computer forensics arena. Computer Forensics Inc. (2005), located in Seattle, Washington is a firm specializing in forensic investigation and discovery. They pioneered the fields of electronic media discovery and electronic risk control in the early 1990s (¶ 1). They have a complete forensics lab in Seattle and the capability for onsite data capture anywhere in the world. They provide the nations largest companies and top law firms with a comprehensive approach to electronic discovery planning, cost management, and data review (Computer Forensics, 2005, ¶ 2). They do one thing: computer forensics. Related CompanyA related company is a medium to large enterprise that specializes in a related field, such as data recovery, and also offers computer forensics goods or services. The largest company in the industry is Kroll Ontrack, Inc. They are a part of Kroll Inc. (Corporate Growth Report, 2002, p. 11854), which is an operating unit of Marsh Inc., the risk and insurance services subsidiary of Marsh & McLennan Companies, Inc. from New York (Kroll, 2006, ¶ 5). Kroll Ontrack specializes in data recoverythey are the worlds experts in this field. Their claim of being the recovery industrys largest, most experienced and technologically advanced provider of data recovery products and services (Kroll, 2006, ¶ 1) has gone unchallenged by other members of the industry. Because of their expertise in this area, they were able to refine their data recovery techniques and offer computer forensics services. Computer crime is a significant problem. Golubev (2004) asserts that economical losses from computer crimes are significant. He observed that damage caused by computer crimes is equal to any advantages gained by the use of computers in business, and we can not estimate social and moral damage at all (¶ 14). An indicator of the magnitude of computer crimes was the existence in 2004 of more than 500 legal documents in the U.S. and 100 plus legal documents in the European Union dealing with information security and computer crimes (Golubev, 2004). Even with the proliferation of so many attempts to define and control computer crimes, Golubev (2004) concludes that these efforts still are inadequate. Defining Computer CrimesA continual challenge for governments and law enforcement agencies is to define computer crimes. This moving target is a management challenge for the computer forensics industry. One example is trying to prove that bad stuff on someones hard drive is their responsibility (Naumov, 2003). During the early days of computer forensics, the only proof of malfeasance was the existence of evidence on a hard drive. Today it is possible to store almost anything on a remote computer without the owners knowledge. (The details of remote storage, while interesting, are not the topic of this paper.) In addition to discovering the evidence, todays computer forensic examiners may need to demonstrate how data got on the hard drive. Unauthorized access to a protected computer system is an example of a computer crime. Computer forensics investigators are able to find the smoking gun of unauthorized files on a criminal's computer and document a digital bread crumb trail to prove unauthorized access. In February 2006, based on computer forensic evidence, Scott Levine was sentenced by a federal court to 96 months in federal prison for 120 counts of unauthorized access of a protected computer, two counts of access device fraud, and one count of obstruction of justice (Department of Justice, 2006, ¶ 1). Brian Marr, Special Agent in Charge of the Little Rock office of the U.S. Secret Service warns would-be computer criminals that neither the Internet nor cyberspace will ever be a safe haven for individuals who attempt this type of cyber crime. The Secret Service, along with our law enforcement partners, will hunt you down, keystroke by keystroke, until you face a jury of your peers (Department of Justice, 2006, ¶ 4). Finding Qualified StaffAs with any industry, people are one of the most significant components of success for the computer forensics industry. In any emerging industry, it is difficult finding people qualified to do the job. One of the most serious problems faced when attempting to establish a computer forensic facility is the lack of trained and skilled staff. There are no full time training facilities providing streams of computer forensic graduates, and nor will there be for many years to come. There are few technical people with training in investigations, and fewer still with knowledge of forensics. Therefore, no matter how ambitious the project, it will fail unless a solution can be found to this problem. (DIBS, 2006, ¶ 8) A unique difficulty in finding qualified staff in the computer forensics industry is that many of the leading professionals are employed by government agencies (e.g., NSA or CIA) or law enforcement personnel. So, even if they can gain authorization to publish their work, likelihood is it isn't published under their actual name (Potaczala, 2001, p. 2) Frequently, those who are qualified may be overworked. An observation by an anonymous poster to Computer Forensics World Forum (http://www.computerforensicsworld.com/modules.php?name=Forums&file=viewtopic&t=102) is that one of his friends works in forensics and he is on call often, and works 65-75 hours per week (¶ 3). There is a likely possibility that this work stress may reduce the number of qualified individuals as those overworked individuals seek other less demanding professions. There simply are not enough people to do this work, says Scott Pancoast, a Seattle-based certified forensic computer examiner with the Washington state Attorney General's Office (Monson, 2002, ¶ 3). Law enforcement and government agencies always have snapped up graduates from university computer forensics programs, but demand is booming now that private companies have begun recruiting cyberinvestigators (Eckle, 2006, p. 54). Marcus K. Rogers, an associate professor in charge of the computer forensics program at Purdue University's College of Technology reports that demand has gotten so great that graduates in the field are some of the most sought after in the country this year (Eckle, 2006, p. 54). In the 1940s and early 1950s human relations practices typically postulated that the feelings of people were more important than the logics of organizational charts, rules, and directives (Wren, 2005, p. 367). Todays managers in the computer forensics industry must keep that in mind when they balance the business needs against the shortage of people. A reduction in an already scarce population of qualified workers adds additional personnel management and retention challenges. History teaches us that labor turnover carried a high cost, both for the employee and the employer, and scientific management sought to reduce that waste of resources (Wren, 2005, p. 241). Industry managers who learn from history and apply the appropriate scientific management techniques to their situation have a higher probability of remaining in business that those who ignore the I-did-it-the-hard-way lessons of management history. Educating the PlayersAnother challenge faced by the computer forensics industry is educating the public who do not understand the industry and well-meaning professionals who occasionally destroy crime scene evidence unintentionally. Even if they do not destroy the evidence, they may not use the proper methods for obtaining data and make their retrievals inadmissible in court, or worse, do something that could be considered a criminal act (Potaczala, 2001, p. 31). Some lawyers do not know how to evaluate the testimony of an expert witness. During an interview about computer forensics, Potaczala (2001) asked Sgt. Kevin Stenger, a computer forensics expert from the Orange County Sheriffs Office, When testifying in court or during a deposition for a computer investigation, what common ways have lawyers used to discredit your investigation (p. 39)? Sgt. Stengers response was revealing: Computer Forensics is still new to the legal community. On my first and to date only deposition I was excused by the attorney who stated that he did not know what questions to ask me (Potaczala, 2001, p. 39). Managers face a challenge to educate their employees about the public nature of private e-mail messages. It is important for employees to understand they have no reasonable expectation of privacy (Sutton, 2003, p. 9). Even after e-mail messages have been deleted from a senders computer, they may still reside on the receivers computer. For a time, they also will reside on the e-mail server and any server between the sender and receiver. This is a security area managers in the past did not have to manage. In the past, it was relatively easy to control the number of copies created and the location of all copies of a sensitive document. Today, however, an e-mail message containing sensitive information could end up almost anywhere. Carr and Williams (1994) exhort the business community to be aware that senior management must accept that computer crime poses a real threat and impost cost effective measures for its prevention (p. 147). The computer forensics industry must educate the general business community of the dangers of computer crime and offer them a solution to this problem. Computer forensics can disclose the source of many computer crimes and reveal evidence the perpetrators of crimes thought they had destroyed. Each challenge faced by the industry has the potential for a great opportunity. Successful managers recognize how to turn each challenge into a specific opportunity. Monson (2002) observed that the Carnegie Mellon Software Engineering Institute recorded only six computer/network security incidents in 1988, while posting 52,658 in 2001 (¶ 9). That amount more than doubled over the next two years, jumping to 137,529 in 2003 (CERT, 2006, ¶ 8). The trend is persistent today as incident reporting continues to escalate. As security incidents and the use of computers for criminal cases increases, so does the business opportunity. Computer forensics managers must be poised to take advantage of this growing demand for their services. Technological change disrupts the social system, a factor that should be considered in any initiation of change by management (Wren, 2005, 338). As changing technology increases business opportunities it also increases the challenge to find qualified workers and manage the change faced by current workers. Training OpportunitiesAs the demand for trained staff continues to increase, so do the opportunities for companies to provide training. Major universities now offer courses related to computer forensics at both undergraduate and graduate level. Computer forensics firms are expanding their services by not only conducting investigations, but also teaching others to do the same. The managers of companies developing training programs are adding both new business opportunities and qualified investigators to the industry. An example of a training organization that exists because of this emerging industry is the National Center for Forensic Science (NCSF). It was founded in 2005 by the National Institute of Justice and hosted by the University of Central Florida. NCFS provides research, education, training, tools and technology to meet the current and future needs of the forensic science, investigative and criminal justice communities (NCSF, 2006, ¶ 8). NCFS offers a Graduate Certificate in Computer Forensics. Expanded Business OpportunitiesAs the computer forensics industry grows, it provides the opportunity to create new businesses and expand opportunities for existing companies. Two examples of new industry players are ADR Data Recovery (existing business) and Technology Pathways (new business). ADR Data Recovery (formerly American Data Recovery, Inc.) started in 1995 (ADR, 2006, ¶ 2). They began business recovering lost data from computers and seamlessly evolved to include computer forensics services. From their headquarters in Folsom, CA, they manage more than 12 Regional Labs and 19 Service Centers (ADR, 2006, ¶ 5). Technology Pathways (2006) opened its doors for business in September 2001 to offer a software product that aided computer forensic investigators (¶ 1). Over the past three years, it has emerged as one of the leaders in this rapidly growing market (Technology Pathways, 2006, ¶ 1). Shortly after the company started, the management team recognized and exploited a new business opportunity in remote forensics, which would revolutionize the way that forensics is utilized and open up new and broader applications (Technology Pathways, 2006, ¶ 4). Steve Richardson, the companys President and CEO has used his Harvard Business School MBA training and more than 25 years of practical experience to steer the company in the right direction (Technology Pathways, 2006, ¶ 8). Information management practitioners also have a new business opportunity since the emergence of computer forensics. In the past, information managers were concerned mostly with paper products, file folders, filing cabinets, and so forth. Today, they also are concerned with electronic storage media, since computer documents can be spread over numerous physical locations, not to mention numerous magnetic storage devices within any one location (Caloyannides, 2004, p. 315). Keeping track of this data and teaching others how to manage their vast resources of electronic records is a new service offering for information management firms. Other examples of specific business opportunities available for computer forensic examiners are: security auditing, drive sterilization, Internet history analysis, and e-mail and chat recovery. (See Figure 2) 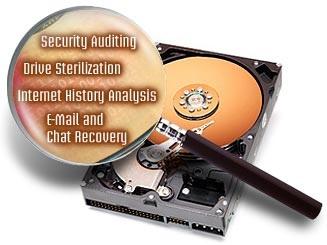
Figure 2. Business opportunities for forensic examiners. (Starken, 2005) Sterneckert (2004) documented several best practice policies and procedures for critical incident management. He suggests that organizations today must have policies regarding when computer forensics examiners should be called in (p. 81). Indirectly, the emergence of the computer forensics industry has created new business opportunities for policy writers and management consultants. As managers learn about and appreciate the importance of computer forensics, they can turn to policy writers to assist them in developing company policies and procedures to include computer forensics. Quality of Service OpportunitiesA unique opportunity not shared by many other industries is that, generally, quality of service is more important than the cost of the service. Thomas Moore, Director of Computer Forensics for TKM Technologies Ltd. in the United Kingdom, offers his professional opinion that reflects his belief that quality of service is more important than price: I believe that computer forensics remains a largely incident-response orientated service. The issues at stake are often very significant - in both criminal and commercial forensics. As such, many clients are less sensitive to price and are often more concerned with response times, quality of results and discretion. (Moore, 2006, ¶ 1) Court records and new laws in the United States highlight that the failure of an organization to retain electronic documents and to be able to locate the information when needed can cost the organization millions of dollars as well as its reputation (Luoma, 2006, p. 91). When faced with a life-threatening condition to the business, todays managers are more concerned with the ability to recover certain information than they are in the cost of recovery. The cost for irretrievably lost data frequently is much more expensive that the cost to hire a successful forensic examiner. Companies able to recover and preserve obscure digital information that meets evidence requirements of our legal system will continue to thrive. A specific area where management has the opportunity to make improvements is in the way the industry processes data. Walton (2005) believes that in the current state of practice, security properties of software systems are assessed through error-prone, labor-intensive human evaluation (¶ 1). The first computer forensics company that develops the ability to reduce errors and the time involved in recovering data will take a big leap forward in the industry. What other big leaps can be expected from the computer forensics industry? Thomas Longstaff, Deputy Director of Technology, CERT Program shares his glimpse of the future for computer security: Beyond today's world, we visualize software in new generations of ubiquitous computing and communication products, many of which we will not immediately recognize as networked computers. Cell phones provide a glimpse into this developing world by placing in our hands a combined audio-visual communications devise, network browser, secure purchasing agent, geographic locator, gaming and entertainment system, and trusted wallet. We will see similar capabilities in cars, homes, offices, and more systems unimaginable today. All will be enabled by software and, in our vision, all will be subject to a full understanding of their behavior as a basis for engineering security into their operational features. (Longstaff, 2005, p. 1) History reveals the successes of companies that took advantage of changing technologies and markets by designing the appropriate business structures to exploit those emerging markets (Wren, 2005, p. 454). Future history will unveil as of yet unknown companies that were able to adapt successfully to the detailed understanding and effective application of Longstaffs more systems unimaginable today. The problem of crime definition will continue in the future. Will it be a crime to have the wrong things stored on your electronic shopping list automatically created by your refrigerator? In the not-so-distant future, stores will be able to access information stored in your refrigerator and supply you with just-in-time products. It sounds like science fiction, but new technology being introduced at NPE [National Packaging Expo] 2006 by HEKUMA GmbH of Eching, Germany, paves the way for just such a development (Lyons Media, 2006, ¶ 1). What would happen if a criminal hacked into your refrigerator shopping list and posted information about drug dealer contacts in your neighborhood? How would you answer embarrassing questions from a police detective about why you have that information in your possession? An aspect of successful business management is risk management. Vacca (2005) teaches that the best approach for organizations wanting to counter cyber crime is to apply risk-management techniques (p. 156). In the future, successful companies will include computer forensics capabilities in their risk management planning. Vacca (2005) proposes that the management of cyberterrorism risk must be considered an important issue for all aspects of society, not only for private companies (p. 503). In the future, successful managers will make computer forensics part of their risk management portfolio. Todays business enterprises are less formal than they were during the Industrial Revolution. A significant cause for this informality is the use of e-mail. Early firms insulated upper management from individual workers with several layers of mid-level managers. Today, e-mail has effectively allowed anyone to bypass the hierarchy and protocol and contact anybody else directly (Caloyannides, 2004, p. xvi). This trend will continue into the future. Perhaps in the future, each employee will have a video conference system in their cubical and we will leave video mail instead of e-mail. Forensic examiners will need to deal with an increasing amount of digital data labeled as official business documentation. The future computer forensics industry may see the extinction of sole practitioners. As the industry becomes more complicated and demands for computer forensic services increase, the sole practitioner may not be able to compete with larger firms. To succeed in the future, sole practitioners must become narrow specialists and be recognized as the best at what they do. There will be plenty of niche market opportunities for the one-man show if the practitioner does not try to expand too far and explode like a balloon filled beyond its capacity. Except for integrating computer forensics techniques into normal management practices, there will not be any significant unique management characteristics emerging in the computer forensics industry. Individual companies which offer computer forensics services will succeed if they follow best practice management techniques for a company of their size and location. However, methods of managing information in the future will exceed the imagination of most current observers and can be the subject of another article. Final questions to ponder: What if someone invents an operating system or software application that uses artificial intelligence methods to automatically archive and organize everything entered into the computer system? Will there be a need for computer forensics if nothing could be hidden or deleted? If so, will that give birth to a new industry that is able to destroy the once digitally indestructible? The good news is that the 21st century has nurtured the emergence of a new industry: computer forensics. The bad news is the reason why the computer forensics industry is flourishing: computer crimes. As computer crimes continue to grow, so must the responses from business managers. The computer forensics industry is poised to assist business managers and the court system control and contain the computer crime threat. Challenges facing the computer forensics industry have created new opportunities for existing businesses and spawned new organizations. Sole practitioners, specialized companies, and related firms are taking advantage of those new opportunities to offer computer forensic services. Training, expanding business, and customer service are three opportunities ripe for picking in the computer forensics industry. Managers who identify and exploit those opportunities will see their firms flourish. What does the future hold for the industry? Thomas Longstaff, Deputy Director of Technology, CERT Program (2005), gives us a glimpse of the future with its prediction that more systems unimaginable today (p. 1) will be waiting for us there. Evolution of computer forensics industry management practices will parallel main-stream business enterprises to meet future challenges. Additionally, as Wren (2005) proposed, the industry must develop dynamic capabilities that will enable it to transform itself as competitive conditions change (p. 422). ADR. (2006). About us: About ADR. Retrieved July 24, 2006, from http://www.adrdatarecovery.com/about_us/index.html Armor Forensics. (2005). Computer forensics defined. [Electronic version]. Jacksonville FL: Author. Retrieved July 21, 2006, from http://www.forensics-intl.com/def4.html Berryhill, J. (2005). Discovering facts -- Delivering results. Retrieved July 24, 2006, from http://www.computerforensics.com/services.htm Caloyannieds, M. A. (2004). Privacy protection and computer forensics. Boston: Artech House. Carr, I. & Williams, K. (Eds.). (1994). Computers and law. Oxford, England: Intellect. CERT. (2006). Incidents reported: 2000-2003. Retrieved July 21, 2006, from http://www.cert.org/stats/cert_stats.html Computer Forensics Inc. (2005). Who we are. Retrieved July 25 2006, from http://www.forensics.com/html/company_who.html Corporate Growth Report. (2002, April 8). Kroll Inc. to purchase Ontrack Data International for 2.5 times revenue. Weekly Corporate Growth Report, 1184, p 11854. Department of Justice, United States. (2006). Former officer of Internet company sentenced in case of massive data theft from Acxiom Corporation. Retrieved July 27, 2006, from http://www.cybercrime.gov/levineSent.htm DIBS USA Inc. (2006). The DIBS methodology. Retrieved July 14, 2006, from http://www.dibsusa.com/methodology/methodology.asp Eckle, J. (2006, May 22). Cybersleuths getting top dollar. Computerworld, 40(21), 54. Golubev, V. (2004). Information protection in automated systems. [Electronic version]. Zaporozhye, Ukraine: Computer Crime Research Center. Retrieved July 21, 2006, from http://www.crime-research.org/articles/Information_protection_automated_systems/2 Hall, E. V. (2006). Computer forensics and its impact on employment litigation: Finding the "smoking gun." [Electronic version]. Denver, Co: Rothgerber Johnson & Lyons. Retrieved July 14, 2006, from http://www.rothgerber.com/newslettersarticles/le0061.asp Kroll Ontrack. (2006). Ontrack Data Recovery company overview. Retrieved July 24, 2006, from http://www.ontrack.com/overview/ Longstaff, T. (2005). CERT research: 2005 annual report. [Electronic version]. Pittsburgh, PA: Software Engineering Institute, Carnegie Mellon University. Retrieved July 21, 2006, from http://www.cert.org/archive/pdf/cert_rsch_annual_rpt_2005.pdf Luoma, V. M. (2006, March). Computer forensics and electronic discovery: The new management challenge. [Electronic version]. Computers & Security, 25(2), 91-96. Lyons Media, Inc. (2006). In-mold labels that hide RFID tags. Retrieved July 27, 2006, from http://www.packagedesignmag.com/issues/2006.06/inthenews.shtml Michailov, I. (2006). ComputerForensics.jpg [Image]. Retrieved July 21, 2006, from http://computer-forensics-lab.org/ Monson, S. (2002). Computer forensics specialists in demand as hacking grows. Zaporozhye, Ukraine: Computer Crime Research Center. Retrieved July 21, 2006, from http://www.crime-research.org/news/2002/09/Mess1002.htm Moore, T. (2006). The forensics industry. A response posted on the Computer Forensics World Forum. Retrieved on July 21, 2006, from http://www.computerforensicsworld.com/modules.php?name=Forums&file=viewtopic&t=281 Naumov, V. (2003). Liability for computer crime in Russia. [Electronic version]. St. Petersburg, Russia: Russian Law Net. Retrieved July 21, 2006, from http://www.russianlaw.net/english/ae07.htm NCFS (National Center for Forensic Science). (2006). Welcome to the National Center for Forensic Science's home page. Retrieved July 24, 2006, from http://www.ncfs.org/ Potaczala, M. (2001). Computer forensics. [Electronic version]. Unpublished paper, University of Central Florida, Orlando. Retrieved July 26, 2006, from http://chantry.acs.ucf.edu/~mikep/cf/CHS5937-TermPaper.pdf Robbins, J. (n.d.). An explanation of computer forensics. Retrieved July 25, 2006, from http://www.computerforensics.net/forensics.htm Secret Service, United States. (Ed.). (2006). Best practices for seizing electronic evidence. A joint project of the International Association of Chiefs of Police and the United States Secret Service. Retrieved July 19, 2006, from http://www.secretservice.gov/electronic_evidence.shtml Starken Group. (2005). Computer forensics services. [Image]. Retrieved July 25, 2006, from http://www.starken.com/modules/ContentExpress/img_repository/computer-forensics-services.jpg Sterneckert, A. B. (2004). Critical incident management. Boca Raton, FL: Auerbach. Sutton, N. (2003, June 6). Privacy laws demand records management. [Electronic version]. Computing Canada, 29(11), 1, 9. Technology Pathways. (2006). About Technology Pathways. Retrieved July 24, 2006, from http://www.techpathways.com/DesktopDefault.aspx?tabindex=1&tabid=2 Vacca, J. R. (2005). Computer forensics: Computer crime scene investigation (2nd ed.). [Electronic version]. Hingham, MA: Charles River Media. Walton, G. (2005). Computational security attributes: Engineering automation for security assessment. [Electronic version]. Pittsburgh, PA: Software Engineering Institute, Carnegie Mellon University. pp. 29-30. Retrieved July 21, 2006, from http://www.cert.org/archive/pdf/cert_rsch_annual_rpt_2005.pdf Wren, D. A. (2005). The history of management thought (5th ed.). Hoboken, NJ: Wiley. |
||||
|