 |
Interesting Articles about Popular Topics |
|
|
Dave Carlson - November 7, 2006 Paul Williams makes many points related to terrorism and gang activity in his book, The Al Qaeda Connection: International Terrorism, Organized Crime, and the Coming Apocalypse. This article discusses five points from the book. It compares and contrasts Williams views with those of other authors then formulates a conclusion related to each of the five points. The points are: 1) Bin Laden and the Chechen Mafia have a close relationship; 2) Al Qaeda has established a significant presence in South America; 3) Mara Salvatrucha, a violent gang from El Salvador, is firmly rooted in the United States; 4) Muslim extremists have taken over Mosques in the United States; and 5) The United States faces an imminent nuclear nightmare from al Qaeda. Paul Williams makes many points related to terrorism and gang activity in his book, The Al Qaeda Connection: International Terrorism, Organized Crime, and the Coming Apocalypse. This article will discuss five points taken from the last four chapters of the book. It will compare and contrast Williams views with those of other authors, then formulate a conclusion for each of the five points. 1. Williams (2005): Terrorist organizations use suicide bombers (p. 128). All authors cited agree that terrorist organizations use suicide bombers to accomplish their objectives. Zedalis (2004) suggests that the suicide bomber is todays weapon of choice for many terrorist organizations (p. 1). Some scholars believe that suicide bombers were employed as early as the 11th Century. The Assassins (Ismalis-Nizari), Muslim fighters, adopted suicide terrorism as a strategy to advance the cause of Islam. These perpetrators perceived their deaths as acts of martyrdom for the glory of God (Sprinzak, 2000, p. 68). A significant difference between the Assassins of antiquity and todays suicide bombers appears to be a divergence in philosophy. Unlike todays suicide bombers, the Assassins murdered particular individuals rather than randomly targeting people whose only crime is to be in the wrong place at the wrong time (Stern, 2003, p. xxiii). Williams (2005) shares recent history of suicide bombers when he shared the first Hamas suicide bombing came on April 13, 1994 in a Hadera bus station (p. 128). Hamas is a Sunni terrorist group opposed to all attempts to make peace with Israel. They received instruction from Hezbollah in advanced bomb-making techniques and tactics involving suicide bombers (Williams, 2005, p. 128). Abu Shanab, Hamas leader, acknowledged that there are some things an organization is not able to teach. He stated that all that is required is a bomb, a detonator, and a moment of courage; and courage is the scarce resource (Stern, 2003, p. 40). In addition to courage, analysts agree that a significant ingredient in the formula for success suicide bombings is a strong religious conviction that the suicide bomber is doing the right thing. It is interesting to note that the Sunnis believe the Koran prohibits suicide (inithar) in any form. However, Sunnis also believe that there is a significant reward for martyrdom (istishad), including the forgiveness of all their sins (including suicide). While each action results in death, the distinction between inithar (suicide resulting from personal distress) and istishad (to give ones life in the name of Allah) is in what happens after death (Hudson, 1999, p. 34). Upon death, all martyrs are immediately welcomed into heaven and provided with every pleasure God has created for mankind to enjoy (Zedalis, 2004, p. 9). The Koran (22:58) states: And (as for) those who fly in Allah's way and are then slain or die, Allah will most certainly grant them a goodly sustenance, and most surely Allah is the best Giver of sustenance. Suicide bombers also are taught that they are true defenders of the oppressed and dispossessed (Howard & Sawyer, 2002, p. 129). Stern (2003) suggests that suicide bombings are increasing, especially among the youth, because they are starting to accept martyrdom as a natural and honorable part of their culture. Ordinary suicide has been shown to spread through social contagion especially among youth. Studies have shown that a teenager whose friend or relative commits suicide is more likely to commit suicide himself. Suicide bombing entails a willingness not only to die, but also to kill others. The situation in Gaza suggests that suicide-murder can also be spread through social contagion. Martyrdom operations are part of the popular culture. For example, on the streets of Gaza, children play a game called shuhada, which includes a mock funeral for a suicide bomber. Teenage rock groups praise martyrs in their songs. Asked to name their heroes, young Palestinians are likely to include suicide bombers (p. 52-53). It is impossible to know exactly why someone decided to make the ultimate sacrifice and intentionally destroyed himself and other humans occupying the same time and space. Following a successful attack, there remains no eye-witness to the thought process triggering the irrevocable decision to push the button. Hudson (1999) is confident in his assertion that terrorist suicide bombers are neither psychopathic nor mentally sick. Contrary to the stereotype that the terrorist is a psychopath or otherwise mentally disturbed, the terrorist is actually quite sane, although deluded by an ideological or religious way of viewing the world (p. 60). One needs only to read or watch the news these days to come to a conclusion that suicide bombings are increasing and are devastatingly effective. Suicide bombs are precision-guided munitions controlled by the most sophisticated computer ever known: the human mind. In the words of Ramadan Shalah, Secretary General of Hamas, . . . human bombs cannot be defeated, not even by nuclear bombs (Wyne, 2005, ¶ 6). 2. Williams (2005): Al Qaeda has a significant presence in South America (p. 143). One of the most dangerous locations on the terrestrial portion of the planet is located in South America. This location is known as the Triangle, a border junction between Paraguay, Brazil, and Argentina (Williams, 2005, p. 120). The three cities that make up the Triangle are Ciudad Del Est in Paraguay (formerly Puerto Presidente Stroessner), Foz do Iguaçu in Brazil, and Puerto Iguaçu in Argentina. The most dangerous critter in this part of the world is not a snake that slithers on its belly; rather it is a snake that walks on two legs. The Triangle is the center of just about every kind of illegal activity imaginable. The murder rate in the city of Foz do Iguaçu averages 250 homicides per year, along with hundreds of mysterious disappearances (Williams, 2005, p. 123). Duarte (2006) cited the intelligence service stratfor.com when he identifies the area as a place frequented by Hezbollah and Hamas, two well-known terrorist organizations (¶ 15). The alleged activities of the organizations include money-laundering, counterfeiting operations, and maintaining a logistics and transshipment base (¶ 15). He further identifies al Qaeda as one of the jihadist terror organizations spreading and adapting to counterterrorism efforts (¶ 19) in the South American Triangle. Curtis (2003) refers to the area as The Triborder Area (TBA), which includes Argentina, Brazil, and Paraguay (p. 173). The TBA provides a haven that is geographically, socially, economically, and politically highly conductive for allowing the activities of organized crime, Islamic terrorist groups, and corrupt officials (p. 173). The area is supported by the trafficking of drug and arms, money laundering, as well as an assortment of other lucrative criminal activities (p. 173). Among the Islamic terrorist groups intertwined with criminal activities in the TBA, Curtis (2003) lists al Qaeda, Hizbollah, Islamic Jihad, and al-Muqawamah (p. 174). Corrupt officials and lax immigration controls have made it relatively easy for these organizations to purchase false identity documents, including passports and visas (p. 174). Paraguayan officials rarely question these false identity documents. A factor complicating any attempt to bring law and order to this region is its highly heterogeneous population. The federal police in Brazil (Policia FederalPF) estimated in 2001 that Foz do Iguaçu included people from at least 65 different nationalities (Curtis, 2003, p. 175). Another contributing factor to the difficulty of controlling the region is the economic influence of organized crimes legitimate business enterprises. While it is impossible to determine the ratio between criminal and legitimate economic contributions, Curtis (2003) estimated that the total economy of Ciudad del Este, one of the TBA cities, is larger than the rest of Paraguay (p. 176). There are no recorded incidents of terrorism within the TBA. Rather, the area is used by terrorist organizations as a safe haven to train and plan their terrorist activities (Curtis, 2003, p. 191). Williams (2005) suggests that Hezbollah (the Party of God) was the first terrorist organization to choose the jungles of South America as a location for a forward operating base in 1983 (p. 123). Hezbollah used this base to train new recruits and raise money to support their jihad against Israel and the United States (p. 123). Common fundraising activities in the TBA include money laundering, remittances, donations, extortion, piracy, drug trafficking, and smuggling (Meehan, 2004, p. 14). A 2003 publicity stunt by the Brazilian city of Foz do Iguaçu featured full-page ads in 30 daily newspapers in Brazil, Argentina, and Chile of a long-bearded man lounging on a sofa. The ads caption was, When he is not blowing up the world, Osama bin Laden enjoys himself (Kyodo, 2003, ¶ 8). The primary theme of the advertising campaign If bin Laden risked his neck to visit Foz do Iguaçu, it means it is worthwhile! Everybody wants to see us. Why havent you come yet? (Kyodo, 2003, ¶ 6) had the opposite affect intended by its creators. Instead of drawing more tourists to the area it appeared to have driven them away. The citys tourist traffic suffered because of the negative connotation of the ads, along with an article in the March 11, 2003 issue of Veja, Brazils top-selling weekly magazine (Kyodo, 2003, ¶ 4). Both the city of Foz do Iguaçu and the Brazilian government have vehemently denied the existence of terrorist operations in the area (Kyodo, 2003, ¶ 21). Additionally, Rubens Barbosa, Brazilian Ambassador to the United States, disagrees that active terrorist organizations are operating within Brazil. Barbosa (2004) states that no concrete evidence has been produced to prove the presence of terrorist organizations (or even the existence of fun-raising activities) in the area (¶ 3). There is sufficient evidence to validate the assertion that the triborder area in South America is a terrorist den of iniquity. The dissenting vote comes from the country of Brazil in the declaration that The Brazilian government is committed to fighting terrorism anywhere in our country. We have never failed to investigate any serious accusation or credible lead regarding the presence of terrorists (Barbosa, 2004, ¶ 5). 3. Williams (2005): Mara Salvatrucha, a violent gang from El Salvador, is firmly rooted in the United States (p. 156). No credible evidence exists to deny the existence of the Mara Salvatrucha gang in the United States. On the contrary; all cited sources support Williams assertion that the gang quickly gained recognition for its violence and business savvy (Williams, 2004, p. 156). Their activities include weapon smuggling and drug trafficking within the United States. Castro (2005) identifies Mara Salvatrucha as one of the largest and most violent street gangs in the United States (p. 7-8). Figure 1 shows gang members in prison. 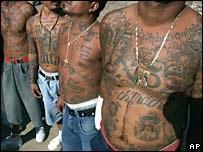
Figure 1. Mara Salvatrucha Gang Members (Image retrieved November 6, 2006 from http://news.bbc.co.uk/1/hi/world/americas/4475240.stm) Originally Mara Salvatrucha, also known as MS-13, was composed exclusively of members born in El Salvador. Today the gang has expanded to include members from Belize, Costa Rica, Ecuador, Guatemala, Honduras, Nicaragua, Mexico (Castro, 2004, p. 5-7), and Panama (Bruneau, 2005, p. 2). From their origin in El Salvador, they expanded through Central America into the United States and Canada. By the early 1990s MS-13 had established a presence in 31 states and the District of Columbia (Castro, 2004, p. 5-11). Their strongest presence is in California, Maryland, New Jersey, New York, Texas, and District of Columbia, with a growing presence in North Carolina (Castro, 2004, p. 11). The National Drug Intelligence Center (NDIC) estimates the MS-13 membership within the United States to be 8,000 to 10,000; worldwide, members and associate members number between 30,000 and 50,000 (Castro, 2004, p. 9). These elaborate and flexible organizations make any attempt to accurately quantify their membership nearly impossible (Bruneau, 2005, p. 3). Williams (2005) supports his assertion that by 2002 the most notorious terrorist organization in the world [al Qaeda] came to a financial agreement with the most violent street gang on the American continent [MS-13] (p. 160) with several logical arguments. However, Bruneau (2005) does not agree. His response is, From all the data I have seen, there is no hard evidence linking the Maras to terrorism (p. 8). Whatever their link to terrorism, there is no argument that MS-13 poses a serious criminal threat to the safety of U.S. citizens. Castro (2004) eloquently synthesizes the MS-13 threat to the United States: Mara Salvatrucha will continue to pose a serious criminal threat to communities throughout the United States. The gangs rapid spread and aggressive recruitment in the United States and in several drug transit and resource countries, coupled with the extreme violence demonstrated by gang members, suggest that Mara Salvatrucha will remain among the most threatening street gang in the country. Indications that previously independent cliques are forming alliances with other Mara Salvatrucha cliques, as well as with other gangs to facilitate criminal activity, further heighten the threat. (p. 44) 4. Williams (2005): Islamic terrorist cells exist in the United States (p. 179). On January 7, 1999, Shaykh Hisham Kabbani, chairman of the Islamic Supreme Council of America, testified before a US State Department committee. Kabbani shared his belief that 80 percent of the mosques in the United States have been taken over by Muslim extremists who are committed to the destruction of the United States (Williams, 2005, p. 177). A group of extremists associated with a terrorist organization is called a cell, a small cadre of zealots whose members know only each other, not members of the larger group (Becker, 2005, p. 394). Becker (2005) identifies two types of terrorist cells: sleeper cell and transit cell. A sleeper cell is comprised of individuals who immigrate, establish a residence and an identity, find employment, and await orders (p. 394), while a transient cell is a group that arrives in a country solely for the purpose of conducting a terroristic [sic] act or campaign (p. 394). An example of a transient cell is the group of terrorists who entered the United States for the sole purpose of coordinating an attack on the United States using hijacked commercial aircraft on September 11, 2001. Williams (2005) asserts that there are Islamic terrorist cells in every major American city and compiles a nefarious roll-call of terrorist organizations with active cells in the United States (p. 179). (See Table 1.)
On May 10, 2000, a copy of the Al Qaeda Training Manual was found in Manchester, England. It was released by the U. S. Department of Justice on December 7, 2001, in accordance with the Freedom of Information Act. A section in the manual listed the guidelines of deportment for sleeper agents in a country of kafirs, such as Great Britain and the United States (Williams, 2005, p. 181).
A suspected al Qaeda terrorist cell was uncovered in 2002. Five members of The Buffalo Six were arrested on September 13, 2002 in Lackawanna, New York. The sixth suspected member of the cell was arrested two days later in Bahrain (Coulson, Benson & Swenson, 2003, p. 92). Prosecutors claimed the six men had attended training in Afghanistan and were awaiting orders from Al Qaeda to carry out a terrorist attack in the United States (Coulson, Benson & Swenson, 2003, p. 92). Facing a lack of evidence in the case, prosecutors found what they needed at the end of an intensive four-day series of negotiations in January 2003. As part of a plea-bargain agreement, 26-year-old Faysal Galab pled guilty to attending one of al Qaedas training camp and agreed to testify against the other five members of the cell in exchange for a reduced sentence (Coulson, Benson & Swenson, 2003, p. 93). Pender (2004) reveals that William Safire uncovered specifics in October 2002 about al Zarquawi setting up al Qaeda sleeper cells in Baghdad to be activated in case the United States defeated Iraq and occupied the city (p. 577). Analysts interpret events surrounding this discovery as an indicator that al Qaeda was working closely with Saddam Hussein (p. 577). The Showtime premium cable channel brought the subject of sleeper cells to the American public in the form of a miniseries entitled Sleeper Cell (Lustick, 2006, p. 38). One theme of the series surrounds a Muslim ex-con being recruited by an Islamic extremist to join a terrorist sleeper cell planning a Los Angeles attack (Lustick, 2006, p. 38). Dramatic events are very effective at getting large populations to think about subjects, in this case, the existence of terrorist sleeper cells in the United States. President George W. Bush warned the American people about Al Qaeda sleeper cells in his 2002 State of the Union address. He said, Thousands of dangerous killers, schooled in the methods of murder, often supported by outlaw regimes, are now spread throughout the world, set up to go off without warning (Williams, 2004, p. 146). There is no disagreement among the authors cited in this section: Terrorist sleeper cells exist in the United States. Al Qaeda training camps teach their sleeper cell recruits to repeat this passage from the Koran several times each day: I will be patient until Patience is worn out from patience (Williams, 2004, p. 157). Our enemy is patient enough to wait until we are not looking before he attacks. Every citizen of the United States must remain vigilant and report activity that may lead to terrorist acts. 5. Williams (2005): The United States faces an imminent nuclear nightmare from Al Qaeda (p. 193). It is interesting to note that there are strong opinions on both sides of this argument. The question is: Does Al Qaeda possess nuclear weapons they plan to use against the United States? Some say yes; some say no. Let us examine the opinion roll call and arguments (see Table 2).
Even though there is an open debate about Al Qaeda possessing nuclear weapons, there does not appear to be any dissent about Al Qaedas willingness to awaken a sleeping United States with a nuclear nightmare. The CIAs Michael Scheuer confirmed in November 2004, that bin Laden had received an Islamic religious determination ruling from Sheikh Hamid bin Fahd that permitted the use of nuclear weapons against the United States of America (Williams, 2005, p. 194). Ferguson (2006) quotes Richard N. Haass, President of the Council on Foreign Relations, when Haass penned the forward to Fergusons study: A nuclear attack by terrorists against the United States has the potential to make the terrorist attacks of September 11, 2001, look like a historical footnote. In addition to the immediate horrific devastation, such an attack could cost trillions of dollars in damages, potentially sparking a global economic depression. (p. v) A consensus among the authors cited in this section is that there are four ways for a terrorist organization to obtain nuclear weapons: purchase, accept as a gift, steal, and build. All authors agree that each of these options is difficult; however, two authors put their marks on the difficulty scale very close to the impossible end. Technical difficulty is listed as a strong argument against the ability of a terrorist organization to possess a nuclear weapon. The facts presented include discussions that range from the difficulty in maintaining a nuclear weapon to the existence of permissive action links (PAL). One version of a PAL can be compared to a super-sophisticated computer passwordif you get it wrong three times your account is locked out. In the case of a nuclear weapon PAL, an incorrect password or sequence of events will render the weapon permanently disabled. It can not be made to function again without replacing specific key components. As representatives of the NO team, Daly, Parachini, & Roseau (2005), send their strongest player forward in the form of the statement that [t]here is no solid evidence that al Qaeda, or indeed any terrorist group, has acquired nuclear weapons, although the desire clearly is there (p. 52). The YES team ably responds to the challenge by sending Williams (2005) forward with a twenty-five page listing of al Qaedas WMD [Weapons of Mass Destruction] Activities (pp. 207-231), including six reports of nuclear weapons purchases. There is no smoking gun to decisively determine the winner of this debate. As of the writing of this paper, no terrorist organization has detonated a nuclear device, nor has any Court in the world admitted a nuclear weapon as evidence against a terrorist organization. However, there is enough credible evidence to suggest it is possible that Al Qaeda might possess one or more fully-functional nuclear devices. This paper compared and contrasted five key points Williams introduced to his readers with views presented by other authors. Some of the authors agreed with Williams, while others offered dissenting opinions. Overall, Williams received a positive nod from his peers. Barbosa, R. (2004, January/February). Triborder dispute. Foreign Affairs. Retrieved November 5, 2006 from http://www.foreignaffairs.org/20040101faletter83165/rubens-barbosa-jessica-stern/triborder-dispute.html Becker, R. F. (2005). Criminal investigation, 2nd Ed. Sudbury, MA: Jones and Bartlett. Bruneau, T. C. (2005, May). The Maras and national security in Central America. [Electronic version]. Strategic Insights, 4(5), 1-12. Retrieved November 7, 2006 from http://www.ccc.nps.navy.mil/si/2005/May/bruneauMay05.pdf Bunn, M. and Wier, A. (2006, September). Terrorist nuclear weapon construction: How difficult? [Electronic version]. The ANNALS of the American Academy of Political and Social Science, 607, 133-149. Retrieved November 3, 2006 from http://ann.sagepub.com/cgi/reprint/607/1/133 Castro, A. J. (2005). Mara Salvatrucha Street Gang: An international criminal enterprise with roots in El Salvadors civil war. [Electronic version]. Department of Homeland Security. Retrieved November 5, 2006 from http://webzoom.freewebs.com/swnmia/Mara.pdf Coulson, D. O., Benson, M., and Swenson, A. A. (2003). The complete idiots guide to national security. New York: Alpha Books. Curtis, G. E. (Project Manager). (2003). Nations hospitable to organized crime and terrorism. [Electronic version]. A report prepared by the Federal Research Division, Library of Congress under and interagency agreement with the United States Government. Retrieved November 7, 2006 from http://www.loc.gov/rr/frd/pdf-files/Nats_Hospitable.pdf Daly, S., Parachini, J., and Roseau, W. (2005). Aum Shinrikyo, Al Qaeda, and the Kinshasa Reactor: Implications for three case studies for combating nuclear terrorism. [Electronic version]. Santa Monica, CA: Rand Corporation. Retrieved November 3, 2006 from http://www.rand.org/pubs/documented_briefings/2005/RAND_DB458.pdf Duarte, J. (2006). South Americas terror financial center. Financial Sense Online. Retrieved November 5, 2006 from http://www.financialsense.com/editorials/duarte/2006/0930.html Ferguson, C. D. (2006). Preventing catastrophic nuclear terrorism. CSR 11. New York: Council on Foreign Relations. Frost, R. (2004). Nuclear terrorism post-9/11: Assessing the risks. [Electronic version]. Global Society, 18(4), 397-422. Howard, R. D. and Sawyer, R. L. (2002). Terrorism and counterterrorism. Guilford, CT: McGraw-Hill. Hudson, R. A. (1999). The sociology and psychology of terrorism: Who becomes a terrorist and why? [Electronic version]. A report prepared under the interagency agreement by the Federal Research Division, Library of Congress. Retrieved November 5, 2006 from http://www.loc.gov/rr/frd/pdf-files/Soc_Psych_of_Terrorism.pdf Kyodo. (2003, April 7). Brazilian city uses Osama bin Laden to draw tourists. Asian Political News. Retrieved November 5, 2006 from http://findarticles.com/p/articles/mi_m0WDQ/is_2003_April_7/ai_99813297 Lustick, I. S. (2006). Trapped in the war on terror. Philadelphia: University of Pennsylvania Press. Meehan, H. V. (2004). Terrorism, diasporas, and permissive threat environments. A study of Hizballahs fundraising operations in Paraguay and Ecuador. [Electronic version]. An unpublished thesis presented to Naval Postgraduate School, Monterey, CA. Retrieved November 6, 2006 from http://www.fas.org/irp/world/para/hizb-fund.pdf Pender, S. (2004). Saddams ties to Al Queda. College Station, TX: Virtualbookworm.com Publishing. Sprinzak, E. (2000, September-October). Rational fanatics. Foreign Policy, 120, 66-73. Stern, J. (2003). Terror in the name of God. New York: Harper Collins. Williams, P. L. (2004). Osamas revenge: The next 9/11 -- What the media and the government havent told you. Amherst, NY: Prometheus Books. Williams, P. L. (2005). The Al Qaeda connection: International terrorism, organized crime, and the coming apocalypse. Amherst, NY: Prometheus Books. Wyne, A. (2005). Suicide terrorism as strategy: Case studies of Hamas and the Kurdistan Workers Party. Strategic Insights, 4(7), a monthly electronic journal produced by the Center for Contemporary Conflict at the Naval Postgraduate School in Monterey, California. Retrieved November 6, 2006 from http://www.ccc.nps.navy.mil/si/2005/Jul/wyneJul05.asp Zedalis, D. D. (2004). Female suicide bombers. Unpublished work submitted to the Army War College. Retrieved November 5, 2006 from http://www.mipt.org/pdf/Female-Suicide-Bombers.pdf Zenko, M. (2006, September). Intelligence estimates of nuclear terrorism. [Electronic version]. The ANNALS of the American Academy of Political and Social Science, 607, 87-102. Retrieved November 3, 2006 from http://ann.sagepub.com/cgi/reprint/607/1/87 |
||||||||||||||||||||||||||||||
|